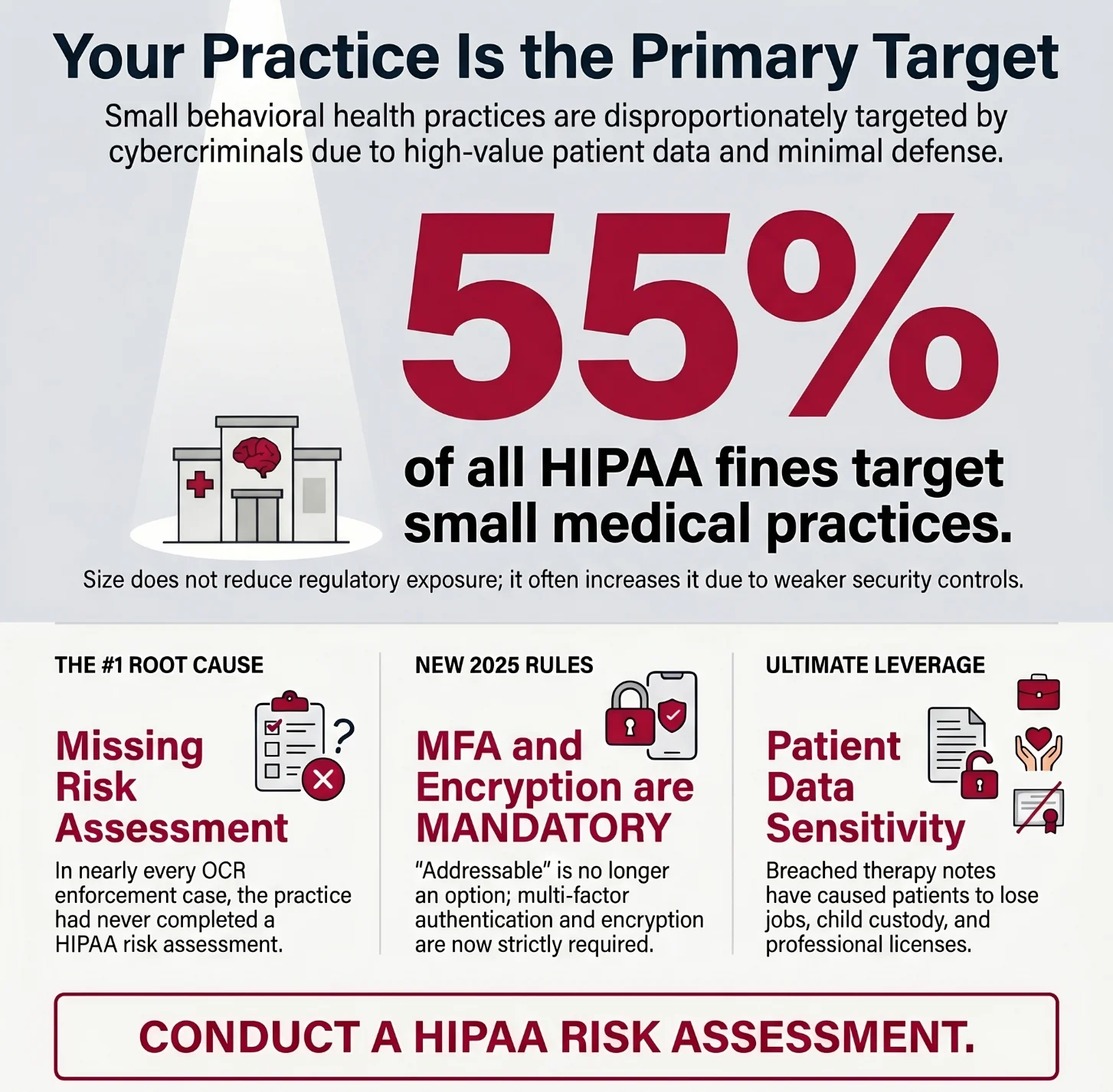
If you run a small behavioral health practice, a therapy group, or a psychiatric clinic, you may assume that cybercriminals are focused on hospitals and health systems. The reality is the opposite. Ransomware groups specifically seek out small behavioral health practices because of what you hold: psychiatric diagnoses, therapy session notes, substance use history, medication records, and the kind of deeply personal patient data that people will pay anything to keep private.
That leverage is exactly what makes you a target. And in most cases, the practices that get hit had no incident response plan, no written security policies, and no one responsible for security at all.
This post breaks down why behavioral health practices are disproportionately targeted, what OCR enforcement actually looks like for small clinics, and what you should do first if you have no IT staff and limited time.
Ransomware operators are businesspeople. They go where the data is most sensitive and where the defenses are weakest. Behavioral health practices check both boxes.
The data is uniquely sensitive. A patient's therapy notes, psychiatric diagnosis, or history of substance use treatment carries a level of sensitivity that goes far beyond a routine medical record. Patients have lost jobs, custody of children, and professional licenses when this information was exposed without their consent. That sensitivity means patients are more likely to pay a ransom to prevent exposure, and that attorneys are more likely to file class actions when a breach occurs.
The defenses are minimal. Most behavioral health practices operate with one to ten clinicians, no dedicated IT staff, and an EHR system that may or may not be configured correctly. Security is typically handled by whoever has the most patience for technology, which is often no one. There are no written security policies, no documented incident response plan, and frequently no signed Business Associate Agreements with billing vendors or telehealth platforms.
OCR knows this. The Office for Civil Rights has been actively targeting small behavioral health practices in its enforcement actions, and the penalties are real.
These are not hypothetical scenarios. These are real practices with real consequences from recent years.
A few things stand out across these cases. First, the practices were small. Second, in almost every case, OCR found the same root cause: no HIPAA risk assessment had ever been conducted. Third, the financial consequences extended well beyond any fine. Corrective action plans require months of documented remediation work, legal fees, and reputational damage that is nearly impossible to quantify.
Understanding how attacks start is the first step toward preventing them. The most common entry points for small behavioral health practices are:
Once a ransomware group gets in, the goal is twofold: encrypt your files so you cannot operate, and exfiltrate sensitive data so they can threaten to publish it if you do not pay. For behavioral health practices, that second threat is often the more terrifying one.
The 2025 HIPAA Security Rule overhaul is the most significant regulatory shift in over a decade, and most small practices have not heard about it. Here is what changed and what it means for you:
At the same time, cyber insurance carriers have tightened their underwriting requirements to mirror these new standards. If you cannot demonstrate MFA, endpoint detection and response (EDR), encrypted backups, and a documented incident response plan, you may face denial of coverage or significant premium increases at your next renewal.
Yes. Full stop.
This is the most common question small practices ask, and the most dangerous misconception in the market. A HIPAA risk assessment is not optional for covered entities, regardless of size. The OCR enforcement cases cited above all share one common finding: no risk assessment had been completed.
A HIPAA risk assessment does not need to be a 200-page enterprise document. For a one-to-five clinician practice, a thorough risk assessment should:
The Cybersecurity Advisory Group HIPAA Readiness Assessment for behavioral health practices is designed specifically for small, owner-operated clinics. It is not a checkbox exercise — it results in a documented security program you can show to OCR, your cyber insurer, and your malpractice carrier.
If your practice has no IT staff and no security program, here is where to start. These are not the only steps, but they are the ones that reduce the most risk in the shortest time.
Step 1: Know where your patient data lives.
List every system that stores or transmits patient data: your EHR, your billing platform, your telehealth tool, your email, your scheduling software. If it touches a patient record, it is in scope for HIPAA.
Step 2: Check your Business Associate Agreements.
Every vendor on that list needs a signed BAA. Many small practices discover they have been sending patient data through billing companies, telehealth platforms, and even email providers for years without a BAA in place. That is an OCR finding waiting to happen.
Step 3: Turn on multi-factor authentication everywhere.
MFA is now required under the 2025 HIPAA updates, and it is one of the single most effective controls against credential theft. Turn it on for your EHR, your email, your billing platform, and anything else on your vendor list.
Step 4: Create a basic incident response plan.
You do not need a 50-page document. You need a written plan that answers three questions: Who do we call when something goes wrong? What do we do to contain it? Who do we notify and by when? Having this documented before an incident is the difference between a manageable situation and a crisis.
Step 5: Conduct a HIPAA risk assessment.
Everything else flows from this. You cannot build a security program without knowing what your risks actually are. If you are not sure where to start, this is the first conversation worth having with a vCISO who specializes in behavioral health practices.
Most small practices do not need a full-time Chief Information Security Officer. A full-time CISO costs $200,000 to $400,000 per year in salary and benefits alone. That is not a realistic option for a practice with five therapists and a part-time office manager.
A virtual CISO provides the strategic security leadership your practice needs at a fraction of that cost. For behavioral health practices specifically, that means:
Cybersecurity Advisory Group works exclusively with small and mid-sized healthcare practices. Behavioral health practices get a vCISO who understands the sensitivity of your patient population, the specific vulnerabilities of your EHR and billing software, and the exact requirements of the HIPAA Security Rule — not a generalist who splits time across finance, tech, and retail clients.
Behavioral health practices hold the most sensitive patient data in healthcare. That is not a reason to panic — it is a reason to take security seriously before a ransomware group, an OCR investigator, or a plaintiff's attorney makes the decision for you.
If you are not sure where your practice stands, the first step is a HIPAA gap assessment. It takes about 15 minutes on the phone to understand your biggest exposure points and what it would take to close them.
Schedule a Free 15-Minute HIPAA Gap Call with Cybersecurity Advisory Group →
Melissa Thornton, CISSP, is the founder of Cybersecurity Advisory Group and a veteran healthcare CISO with experience securing large health systems and building security programs from the ground up for small practices. Cybersecurity Advisory Group serves mental health clinics, dental offices, home health agencies, and specialty practices across the NY/NJ/CT tri-state area.