
The HIPAA Security Rule is about to get its first major overhaul since 2013. The final rule has been sitting on the Office for Civil Rights regulatory agenda for May 2026 release, and whether it lands this month, this fall, or in early 2027, the direction is locked.
Most small healthcare practices have not read it. Many do not know it exists.
The average healthcare data breach for a small practice now costs $250,000 to $1.5 million by the time you add forensics, legal, notification, downtime, and Office for Civil Rights penalties. Civil monetary penalties under the current schedule range from $145 per violation at the lowest tier to over $2.19 million per violation category per year at the willful-neglect-uncorrected tier.
The average healthcare Chief Information Security Officer salary is $200,000 to $450,000.
Most practice owners see those numbers, do the math, and quietly roll the dice. They have an EHR vendor, an MSP, a cyber insurance policy, and a HIPAA training module everyone clicked through last year. So, they move on.
That is the most expensive bet a healthcare owner can make in 2026.
I've spent more than 10 years building security and compliance programs, led multiple HITRUST certification engagements, and deployed Zero Trust architecture across a multi-state clinical operation. Before that, I sat in the CEO seat. I have watched the same pattern play out in small and mid-size healthcare practices for decades: smart owners, capable clinicians, decent IT support, and no one in the room who can turn a pile of tools into a defensible HIPAA program.
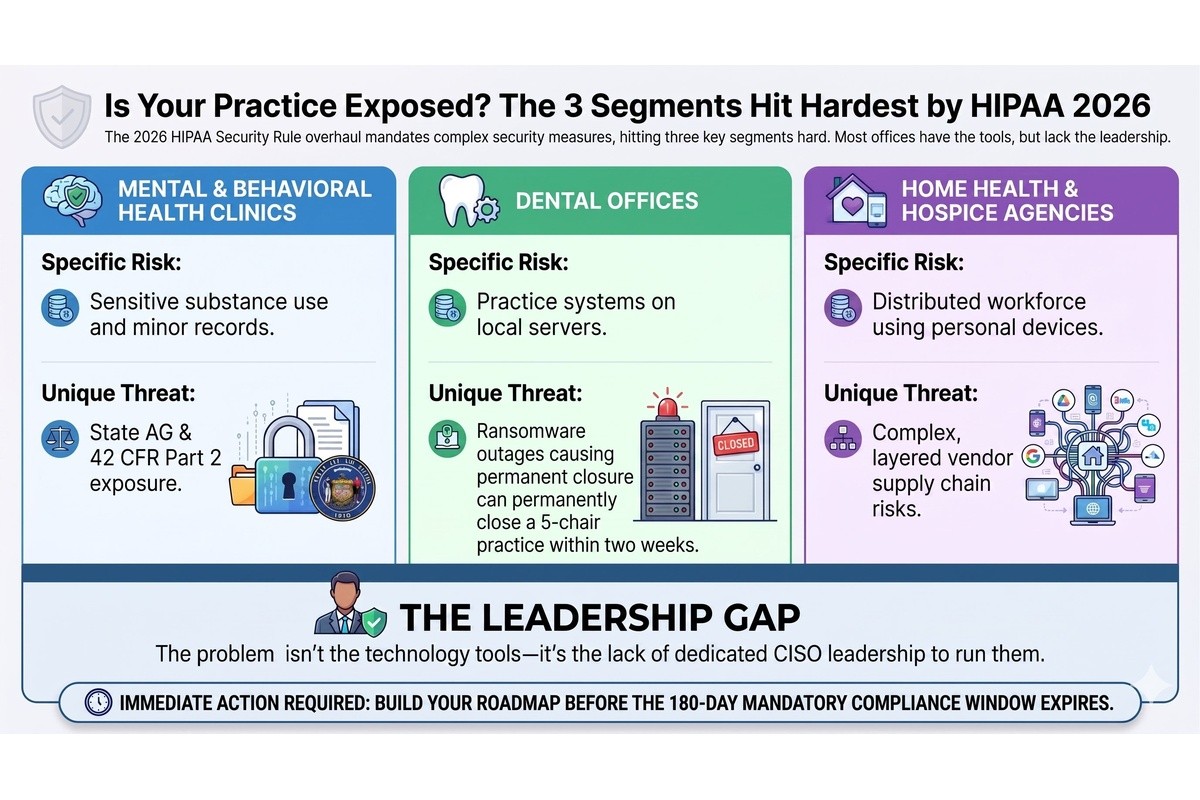
That is the actual gap. It is not technology. It is leadership.
The proposed rule does something the original Security Rule never did. It removes the "addressable" category.
For two decades, the rule split safeguards into two buckets. Required meant you had to do it. Addressable meant you had to consider it and could document why it did not apply. That second bucket gave smaller practices a soft landing. Most of them used it to avoid doing the work.
That bucket is going away.
Under the HIPAA Security Rule 2026 update, the following are no longer optional for covered entities and business associates:
None of these are new ideas. They have been industry best practice for a decade. What changed is that OCR is signaling it will treat their absence as a finding, not a discussion point. Phase 3 HIPAA audits started in March 2025 and are already focused on risk analysis and risk management. Final rule or not, the enforcement posture has shifted.
For a small practice that has been getting by with an MSP, a firewall, and an annual HIPAA training video, this is not a tune-up. This is a structural lift.
Most small healthcare practices already own more security tools than they realize. EHR vendors have access controls. MSPs install endpoint protection. Cyber insurance carriers require MFA. The pieces are usually in place, somewhere, partially deployed, and largely undocumented.
What practices do not have is someone who can do the things tools cannot:
That function is what a Chief Information Security Officer does. And almost no practice under $20 million in revenue has one in-house. The math does not work at that size.
A fractional CISO, also called a virtual CISO or vCISO, provides senior cybersecurity and compliance leadership on a part-time basis. They typically support several organizations at once, which is what makes the economics work.
Instead of $200,000 a year for a full-time hire, a small healthcare practice can engage senior security leadership for a fraction of that. The right vCISO has actually run healthcare security programs, owned HIPAA and HITRUST work end to end, briefed boards, and managed real incidents. They are not a tool reseller in a consultant's jacket.
Fractional CFOs and fractional COOs have been a normal part of the SMB playbook for years. Fractional CISO services in healthcare are catching up, especially as the HIPAA Security Rule 2026 update forces the conversation. The model is not new. The buyer education is.
The HIPAA Security Rule 2026 update hits three small healthcare segments hardest. Different presentation, same underlying problem.
A behavioral health group running on a cloud EHR, a telehealth platform, and a payroll system rarely has a dedicated IT lead, let alone a security function. The data they hold is among the most sensitive in healthcare: substance use treatment, custody-related records, minors in care, and court-ordered services. A breach in a behavioral health practice is not just an OCR event. It is a state attorney general event, a 42 CFR Part 2 event, and frequently a malpractice exposure. Cybersecurity for mental health clinics is one of the most underserved problems in healthcare today, and the new rule does not care that the practice is small.
Dental practices have quietly become one of the most ransomware-targeted segments in healthcare. Practice management systems, imaging archives, and patient databases sit on local servers or single-tenant cloud setups, often with weak backups and no segmentation between the front-desk machines and the clinical systems. HIPAA compliance for a dental practice in 2026 means MFA on the practice management system, encrypted imaging storage, a tested recovery plan, and a current, documented risk assessment. Most dental offices have none of those. A two-week ransomware outage will close a five-chair practice for good.
Home health and hospice run the most distributed clinical workforce in healthcare. Field clinicians use personal phones, agency-issued tablets, point-of-care apps, and a sprawl of vendor-supplied tools to document care in patients' homes. The attack surface is enormous, mobile device management is usually incomplete, and the business associate ecosystem (scheduling, billing, hospice-specific EHRs, DME suppliers) is layered three or four deep. Cybersecurity for home health agencies and hospice providers under the HIPAA Security Rule 2026 update will require real device controls, real vendor oversight, and a real incident response capability. Most agencies are still treating it as an IT issue.
In every one of these segments, the practice owners I talk to understand the risk at some level. They just do not know where to start, and many have already been burned by vendors who sold them tools instead of outcomes.
If the HIPAA Security Rule is the regulatory pressure, cyber insurance is the operational one. Renewal questionnaires in 2026 now ask about MFA coverage, encryption, endpoint detection and response, backup testing, incident response plans, and named security leadership. Practices that cannot answer those questions are getting non-renewed, hit with 40 to 80 percent premium increases, or issued policies with exclusions that effectively negate coverage when it matters most.
Your cyber insurance broker is now the de facto enforcer of cybersecurity standards in small healthcare. If you do not have answers ready before your next renewal, the market will give them to you in the form of a price hike or a denial.
A fractional CISO engagement in a small healthcare practice typically starts with a HIPAA Risk Assessment: what exists, what is exposed, what matters most, and where the gaps are against the 2026 update. From that comes a prioritized roadmap. Not a wish list. A sequenced plan tied to business risk, payer requirements, and insurance renewal timing.
From there the work is unglamorous and high-leverage. Vendor reviews. Business associate agreements that actually get read. Tabletop exercises with the leadership team. HIPAA policies that match how the practice actually operates instead of a template downloaded from the internet. Quarterly briefings to the owner or board in business language. Documentation that holds up under an OCR investigation, a payer credentialing audit, or a Joint Commission survey.
The goal is not to turn a 30-person practice into a hospital security operation. It is to give that practice the leadership function it has been missing, before an incident, an audit, or an insurance renewal forces the issue at the worst possible time.
It is an active enforcement reality. OCR Phase 3 audits are underway. Cyber insurance is already pricing for the new posture. The healthcare ransomware news cycle is not slowing down. And whenever the final rule lands, the compliance clock will be 180 to 240 days, which is a brutal timeline for any practice starting from zero.
The practices that act now will be ready for their next audit, their next renewal, and their next clinical onboarding cycle. The practices that wait will be reading about themselves in a state attorney general press release.
At Cybersecurity Advisory Group, the healthcare clients I work with are not asking whether they have a cybersecurity problem. They know they do. They are asking who can actually run the program for them at a scale that fits a small practice. Owners who have been burned once or twice by vendors selling tools instead of outcomes are particularly fast to recognize the difference.
The fractional CISO model is the answer. It is here, it is affordable, and it works. The market just needs to catch up to the problem.